OpenVPN, Tunnel eingerichtet, Server bzw. Client nicht erreichbar
Hallo Administratoren!
Aus gegebenen Anlass muss ich in unserem Büro mit einem Windows Server 2012 und 4 Clients die Möglichkeit für Homeoffice aus dem Boden stampfen.
Ich habe (meiner laienhaften Meinung nach) die VPN-Verbindung via OpenVPN hergestellt, siehe folgende Logs.
Ich kann aber leider weder vom Server noch vom Client das jew. Gegenstück erreichen.
OpenVPN eingerrichtet lt.:
Easy Windows Guide
Vorhandene Infrastruktur:
Server:
Windows Server 2012 mit statischer IP und OpenVPN
192.168.10.6
Server-Log (CA editiert):
Gateway:
Alte Zyxel Zywall 2
192.168.10.254
Port Forward UDP-Port 1194 auf die IP des Windows-Servers eingerichtet.
Clients in individuellen Netzwerken (Homeoffice)
Client-Log (statische IP-Adresse editiert):
Ping zum Server:
Antwort von 84.116.231.35: Zielnetz nicht erreichbar.
Ping vom Server zum Client:
Zeitüberschreitung der Anforderung
Tracert liefert das selbe.
Firewall wurde zu Testzwecken am Server komplett deaktiviert; lieferte die selben Ergebnisse.
Ich vermute das hier eine Statische Route fehlt, ich stehe aber derzeit komplett an.
Ich wäre für jede Unterstützung dankbar.
Aus gegebenen Anlass muss ich in unserem Büro mit einem Windows Server 2012 und 4 Clients die Möglichkeit für Homeoffice aus dem Boden stampfen.
Ich habe (meiner laienhaften Meinung nach) die VPN-Verbindung via OpenVPN hergestellt, siehe folgende Logs.
Ich kann aber leider weder vom Server noch vom Client das jew. Gegenstück erreichen.
OpenVPN eingerrichtet lt.:
Easy Windows Guide
Vorhandene Infrastruktur:
Server:
Windows Server 2012 mit statischer IP und OpenVPN
192.168.10.6
Server-Log (CA editiert):
Sat Mar 21 18:48:19 2020 MANAGEMENT: CMD 'signal SIGHUP'
Sat Mar 21 18:48:19 2020 SENT CONTROL [ts-laptop]: 'RESTART' (status=1)
Sat Mar 21 18:48:21 2020 C:\Windows\system32\route.exe DELETE 10.8.0.0 MASK 255.255.255.0 10.8.0.2
Sat Mar 21 18:48:21 2020 Warning: route gateway is not reachable on any active network adapters: 10.8.0.2
Sat Mar 21 18:48:21 2020 Route deletion via IPAPI failed [adaptive]
Sat Mar 21 18:48:21 2020 Route deletion fallback to route.exe
Sat Mar 21 18:48:21 2020 env_block: add PATH=C:\Windows\System32;C:\Windows;C:\Windows\System32\Wbem
Sat Mar 21 18:48:21 2020 Closing TUN/TAP interface
Sat Mar 21 18:48:21 2020 NOTE: Release of DHCP-assigned IP address lease on TAP-Windows adapter failed: Dem Endpunkt der Netzwerkverbindung ist noch keine Adresse zugeordnet. (code=1228)
Sat Mar 21 18:48:21 2020 SIGHUP[hard,] received, process restarting
Sat Mar 21 18:48:21 2020 MANAGEMENT: >STATE:1584812901,RECONNECTING,SIGHUP,,,,,
Sat Mar 21 18:48:21 2020 OpenVPN 2.4.8 x86_64-w64-mingw32 [SSL (OpenSSL)] [LZO] [LZ4] [PKCS11] [AEAD] built on Oct 31 2019
Sat Mar 21 18:48:21 2020 Windows version 6.2 (Windows 8 or greater) 64bit
Sat Mar 21 18:48:21 2020 library versions: OpenSSL 1.1.0l 10 Sep 2019, LZO 2.10
Sat Mar 21 18:48:21 2020 Restart pause, 5 second(s)
Sat Mar 21 18:48:26 2020 Diffie-Hellman initialized with 2048 bit key
Sat Mar 21 18:48:26 2020 Failed to extract curve from certificate (UNDEF), using secp384r1 instead.
Sat Mar 21 18:48:26 2020 ECDH curve secp384r1 added
Sat Mar 21 18:48:26 2020 Outgoing Control Channel Authentication: Using 160 bit message hash 'SHA1' for HMAC authentication
Sat Mar 21 18:48:26 2020 Incoming Control Channel Authentication: Using 160 bit message hash 'SHA1' for HMAC authentication
Sat Mar 21 18:48:26 2020 interactive service msg_channel=0
Sat Mar 21 18:48:26 2020 ROUTE_GATEWAY 192.168.10.254/255.255.255.0 I=12 HWADDR=0c:c4:7a:aa:c1:8a
Sat Mar 21 18:48:26 2020 open_tun
Sat Mar 21 18:48:26 2020 TAP-WIN32 device [LAN-Verbindung] opened: \\.\Global\{0C7CEA14-8706-4363-AB2D-BB15E087C96B}.tap
Sat Mar 21 18:48:26 2020 TAP-Windows Driver Version 9.24
Sat Mar 21 18:48:26 2020 Notified TAP-Windows driver to set a DHCP IP/netmask of 10.8.0.1/255.255.255.252 on interface {0C7CEA14-8706-4363-AB2D-BB15E087C96B} [DHCP-serv: 10.8.0.2, lease-time: 31536000]
Sat Mar 21 18:48:26 2020 Sleeping for 10 seconds...
Sat Mar 21 18:48:36 2020 Successful ARP Flush on interface [17] {0C7CEA14-8706-4363-AB2D-BB15E087C96B}
Sat Mar 21 18:48:36 2020 MANAGEMENT: >STATE:1584812916,ASSIGN_IP,,10.8.0.1,,,,
Sat Mar 21 18:48:36 2020 MANAGEMENT: >STATE:1584812916,ADD_ROUTES,,,,,,
Sat Mar 21 18:48:36 2020 C:\Windows\system32\route.exe ADD 10.8.0.0 MASK 255.255.255.0 10.8.0.2
Sat Mar 21 18:48:36 2020 Warning: route gateway is not reachable on any active network adapters: 10.8.0.2
Sat Mar 21 18:48:36 2020 Route addition via IPAPI failed [adaptive]
Sat Mar 21 18:48:36 2020 Route addition fallback to route.exe
Sat Mar 21 18:48:36 2020 env_block: add PATH=C:\Windows\System32;C:\Windows;C:\Windows\System32\Wbem
Sat Mar 21 18:48:36 2020 Could not determine IPv4/IPv6 protocol. Using AF_INET6
Sat Mar 21 18:48:36 2020 Socket Buffers: R=[65536->65536] S=[65536->65536]
Sat Mar 21 18:48:36 2020 setsockopt(IPV6_V6ONLY=0)
Sat Mar 21 18:48:36 2020 UDPv6 link local (bound): [AF_INET6][undef]:1194
Sat Mar 21 18:48:36 2020 UDPv6 link remote: [AF_UNSPEC]
Sat Mar 21 18:48:36 2020 MULTI: multi_init called, r=256 v=256
Sat Mar 21 18:48:36 2020 IFCONFIG POOL: base=10.8.0.4 size=62, ipv6=0
Sat Mar 21 18:48:36 2020 ifconfig_pool_read(), in='ts-laptop,10.8.0.4', TODO: IPv6
Sat Mar 21 18:48:36 2020 succeeded -> ifconfig_pool_set()
Sat Mar 21 18:48:36 2020 IFCONFIG POOL LIST
Sat Mar 21 18:48:36 2020 ts-laptop,10.8.0.4
Sat Mar 21 18:48:36 2020 Initialization Sequence Completed
Sat Mar 21 18:48:36 2020 MANAGEMENT: >STATE:1584812916,CONNECTED,SUCCESS,10.8.0.1,,,,
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 TLS: Initial packet from [AF_INET6]::ffff:80.110.113.67:5269, sid=bbc6516b d3e76dad
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 VERIFY OK: depth=1, "editiert"
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 VERIFY OK: depth=0, "editiert"
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 peer info: IV_VER=2.4.8
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 peer info: IV_PLAT=win
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 peer info: IV_PROTO=2
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 peer info: IV_NCP=2
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 peer info: IV_LZ4=1
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 peer info: IV_LZ4v2=1
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 peer info: IV_LZO=1
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 peer info: IV_COMP_STUB=1
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 peer info: IV_COMP_STUBv2=1
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 peer info: IV_TCPNL=1
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 peer info: IV_GUI_VER=OpenVPN_GUI_11
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 Control Channel: TLSv1.2, cipher TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384, 4096 bit RSA
Sat Mar 21 18:50:11 2020 80.110.113.67:5269 [ts-laptop] Peer Connection Initiated with [AF_INET6]::ffff:80.110.113.67:5269
Sat Mar 21 18:50:11 2020 ts-laptop/80.110.113.67:5269 MULTI_sva: pool returned IPv4=10.8.0.6, IPv6=(Not enabled)
Sat Mar 21 18:50:11 2020 ts-laptop/80.110.113.67:5269 MULTI: Learn: 10.8.0.6 -> ts-laptop/80.110.113.67:5269
Sat Mar 21 18:50:11 2020 ts-laptop/80.110.113.67:5269 MULTI: primary virtual IP for ts-laptop/80.110.113.67:5269: 10.8.0.6
Sat Mar 21 18:50:12 2020 ts-laptop/80.110.113.67:5269 PUSH: Received control message: 'PUSH_REQUEST'
Sat Mar 21 18:50:12 2020 ts-laptop/80.110.113.67:5269 SENT CONTROL [ts-laptop]: 'PUSH_REPLY,route 10.8.0.1,topology net30,ping 10,ping-restart 120,ifconfig 10.8.0.6 10.8.0.5,peer-id 0,cipher AES-256-GCM' (status=1)
Sat Mar 21 18:50:12 2020 ts-laptop/80.110.113.67:5269 Data Channel: using negotiated cipher 'AES-256-GCM'
Sat Mar 21 18:50:12 2020 ts-laptop/80.110.113.67:5269 Outgoing Data Channel: Cipher 'AES-256-GCM' initialized with 256 bit key
Sat Mar 21 18:50:12 2020 ts-laptop/80.110.113.67:5269 Incoming Data Channel: Cipher 'AES-256-GCM' initialized with 256 bit key Gateway:
Alte Zyxel Zywall 2
192.168.10.254
Port Forward UDP-Port 1194 auf die IP des Windows-Servers eingerichtet.
Clients in individuellen Netzwerken (Homeoffice)
Client-Log (statische IP-Adresse editiert):
Sat Mar 21 18:48:17 2020 Connection reset command was pushed by server ('')
Sat Mar 21 18:48:17 2020 SIGUSR1[soft,server-pushed-connection-reset] received, process restarting
Sat Mar 21 18:48:17 2020 MANAGEMENT: >STATE:1584812897,RECONNECTING,server-pushed-connection-reset,,,,,
Sat Mar 21 18:48:17 2020 Restart pause, 5 second(s)
Sat Mar 21 18:48:22 2020 TCP/UDP: Preserving recently used remote address: [AF_INET] "statische IP-Adresse" :1194
Sat Mar 21 18:48:22 2020 Socket Buffers: R=[65536->65536] S=[65536->65536]
Sat Mar 21 18:48:22 2020 UDP link local: (not bound)
Sat Mar 21 18:48:22 2020 UDP link remote: [AF_INET] "statische IP-Adresse" :1194
Sat Mar 21 18:48:22 2020 MANAGEMENT: >STATE:1584812902,WAIT,,,,,,
Sat Mar 21 18:48:59 2020 MANAGEMENT: CMD 'signal SIGHUP'
Sat Mar 21 18:48:59 2020 C:\WINDOWS\system32\route.exe DELETE 10.8.0.1 MASK 255.255.255.255 10.8.0.5
Sat Mar 21 18:48:59 2020 Route deletion via service succeeded
Sat Mar 21 18:48:59 2020 Closing TUN/TAP interface
Sat Mar 21 18:48:59 2020 TAP: DHCP address released
Sat Mar 21 18:48:59 2020 SIGHUP[hard,] received, process restarting
Sat Mar 21 18:48:59 2020 MANAGEMENT: >STATE:1584812939,RECONNECTING,SIGHUP,,,,,
Sat Mar 21 18:48:59 2020 OpenVPN 2.4.8 x86_64-w64-mingw32 [SSL (OpenSSL)] [LZO] [LZ4] [PKCS11] [AEAD] built on Oct 31 2019
Sat Mar 21 18:48:59 2020 Windows version 6.2 (Windows 8 or greater) 64bit
Sat Mar 21 18:48:59 2020 library versions: OpenSSL 1.1.0l 10 Sep 2019, LZO 2.10
Sat Mar 21 18:48:59 2020 Restart pause, 5 second(s)
Sat Mar 21 18:49:04 2020 Outgoing Control Channel Authentication: Using 160 bit message hash 'SHA1' for HMAC authentication
Sat Mar 21 18:49:04 2020 Incoming Control Channel Authentication: Using 160 bit message hash 'SHA1' for HMAC authentication
Sat Mar 21 18:49:04 2020 TCP/UDP: Preserving recently used remote address: [AF_INET] "statische IP-Adresse" :1194
Sat Mar 21 18:49:04 2020 Socket Buffers: R=[65536->65536] S=[65536->65536]
Sat Mar 21 18:49:04 2020 UDP link local: (not bound)
Sat Mar 21 18:49:04 2020 UDP link remote: [AF_INET] "statische IP-Adresse" :1194
Sat Mar 21 18:49:04 2020 MANAGEMENT: >STATE:1584812944,WAIT,,,,,,
Sat Mar 21 18:50:04 2020 TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity)
Sat Mar 21 18:50:04 2020 TLS Error: TLS handshake failed
Sat Mar 21 18:50:04 2020 SIGUSR1[soft,tls-error] received, process restarting
Sat Mar 21 18:50:04 2020 MANAGEMENT: >STATE:1584813004,RECONNECTING,tls-error,,,,,
Sat Mar 21 18:50:04 2020 Restart pause, 5 second(s)
Sat Mar 21 18:50:09 2020 TCP/UDP: Preserving recently used remote address: [AF_INET] "statische IP-Adresse" :1194
Sat Mar 21 18:50:09 2020 Socket Buffers: R=[65536->65536] S=[65536->65536]
Sat Mar 21 18:50:09 2020 UDP link local: (not bound)
Sat Mar 21 18:50:09 2020 UDP link remote: [AF_INET] "statische IP-Adresse" :1194
Sat Mar 21 18:50:09 2020 MANAGEMENT: >STATE:1584813009,WAIT,,,,,,
Sat Mar 21 18:50:09 2020 MANAGEMENT: >STATE:1584813009,AUTH,,,,,,
Sat Mar 21 18:50:09 2020 TLS: Initial packet from [AF_INET] "statische IP-Adresse" :1194, sid=23be88bd 4a24a9bc
Sat Mar 21 18:50:09 2020 VERIFY OK: depth=1, "editiert"
Sat Mar 21 18:50:09 2020 VERIFY KU OK
Sat Mar 21 18:50:09 2020 Validating certificate extended key usage
Sat Mar 21 18:50:09 2020 ++ Certificate has EKU (str) TLS Web Server Authentication, expects TLS Web Server Authentication
Sat Mar 21 18:50:09 2020 VERIFY EKU OK
Sat Mar 21 18:50:09 2020 VERIFY OK: depth=0, "editiert"
Sat Mar 21 18:50:10 2020 Control Channel: TLSv1.2, cipher TLSv1.2 ECDHE-RSA-AES256-GCM-SHA384, 4096 bit RSA
Sat Mar 21 18:50:10 2020 [server] Peer Connection Initiated with [AF_INET] "statische IP-Adresse" :1194
Sat Mar 21 18:50:11 2020 MANAGEMENT: >STATE:1584813011,GET_CONFIG,,,,,,
Sat Mar 21 18:50:11 2020 SENT CONTROL [server]: 'PUSH_REQUEST' (status=1)
Sat Mar 21 18:50:11 2020 PUSH: Received control message: 'PUSH_REPLY,route 10.8.0.1,topology net30,ping 10,ping-restart 120,ifconfig 10.8.0.6 10.8.0.5,peer-id 0,cipher AES-256-GCM'
Sat Mar 21 18:50:11 2020 OPTIONS IMPORT: timers and/or timeouts modified
Sat Mar 21 18:50:11 2020 OPTIONS IMPORT: --ifconfig/up options modified
Sat Mar 21 18:50:11 2020 OPTIONS IMPORT: route options modified
Sat Mar 21 18:50:11 2020 OPTIONS IMPORT: peer-id set
Sat Mar 21 18:50:11 2020 OPTIONS IMPORT: adjusting link_mtu to 1624
Sat Mar 21 18:50:11 2020 OPTIONS IMPORT: data channel crypto options modified
Sat Mar 21 18:50:11 2020 Data Channel: using negotiated cipher 'AES-256-GCM'
Sat Mar 21 18:50:11 2020 Outgoing Data Channel: Cipher 'AES-256-GCM' initialized with 256 bit key
Sat Mar 21 18:50:11 2020 Incoming Data Channel: Cipher 'AES-256-GCM' initialized with 256 bit key
Sat Mar 21 18:50:11 2020 interactive service msg_channel=640
Sat Mar 21 18:50:11 2020 ROUTE_GATEWAY 192.168.0.1/255.255.255.0 I=3 HWADDR=f8:94:c2:fe:66:86
Sat Mar 21 18:50:11 2020 open_tun
Sat Mar 21 18:50:11 2020 TAP-WIN32 device [LAN-Verbindung] opened: \\.\Global\{F9DD8F68-9922-4DFE-AE84-30799FDD0807}.tap
Sat Mar 21 18:50:11 2020 TAP-Windows Driver Version 9.24
Sat Mar 21 18:50:11 2020 Notified TAP-Windows driver to set a DHCP IP/netmask of 10.8.0.6/255.255.255.252 on interface {F9DD8F68-9922-4DFE-AE84-30799FDD0807} [DHCP-serv: 10.8.0.5, lease-time: 31536000]
Sat Mar 21 18:50:11 2020 Successful ARP Flush on interface [22] {F9DD8F68-9922-4DFE-AE84-30799FDD0807}
Sat Mar 21 18:50:11 2020 MANAGEMENT: >STATE:1584813011,ASSIGN_IP,,10.8.0.6,,,,
Sat Mar 21 18:50:16 2020 TEST ROUTES: 1/1 succeeded len=1 ret=1 a=0 u/d=up
Sat Mar 21 18:50:16 2020 MANAGEMENT: >STATE:1584813016,ADD_ROUTES,,,,,,
Sat Mar 21 18:50:16 2020 C:\WINDOWS\system32\route.exe ADD 10.8.0.1 MASK 255.255.255.255 10.8.0.5
Sat Mar 21 18:50:16 2020 Route addition via service succeeded
Sat Mar 21 18:50:16 2020 Initialization Sequence Completed
Sat Mar 21 18:50:16 2020 MANAGEMENT: >STATE:1584813016,CONNECTED,SUCCESS,10.8.0.6, "statische IP-Adresse" ,1194,, Ping zum Server:
Antwort von 84.116.231.35: Zielnetz nicht erreichbar.
Ping vom Server zum Client:
Zeitüberschreitung der Anforderung
Tracert liefert das selbe.
Firewall wurde zu Testzwecken am Server komplett deaktiviert; lieferte die selben Ergebnisse.
Ich vermute das hier eine Statische Route fehlt, ich stehe aber derzeit komplett an.
Ich wäre für jede Unterstützung dankbar.
Bitte markiere auch die Kommentare, die zur Lösung des Beitrags beigetragen haben
Content-ID: 560031
Url: https://administrator.de/forum/openvpn-tunnel-eingerichtet-server-bzw-client-nicht-erreichbar-560031.html
Ausgedruckt am: 04.08.2025 um 23:08 Uhr
7 Kommentare
Neuester Kommentar
Hold Dir eine kleine VPS bei Contabo oder Hetzner. Ubuntu 18.04 drauf mit Wireguard Server. Dann auf alle Clients den Wireguard-Client installieren. Dann die Clients auf dem Wireguard-Server einrichten. Verbinden. Das sind fuer Laien 60 Minuten Arbeit. Anleitungen gibts genug im Netz.
Kein Port-Forwarding oder aehnliches noetig.
Andere Moeglichkeit waere auch ueber ZEROTIER. Ebenfalls einfach fuer Non-Admins einzurichten.
Viel Glueck und Gruesse
Sato
Kein Port-Forwarding oder aehnliches noetig.
Andere Moeglichkeit waere auch ueber ZEROTIER. Ebenfalls einfach fuer Non-Admins einzurichten.
Viel Glueck und Gruesse
Sato
ganz verstehe ich noch nicht, wo welches lokale Netz ist,
aber: 10.8.0.1 ist der Windows-Server über das Tunnelnetz,
10.8.0.6 (dynamisch zugeordnet) ist der VPN-Client,
d.h. ein ping auf den Server sollte gehen und z.B. RDP-Zugang zu diesem auch bereits,
wenn es nur um Datei-Freigaben auf diesem Server geht, bist Du bereits fertig, 10.8.0.1 wird die allen vier Clients zur Verfügung stellen.
Eine weitere statische Route zu 10.8.0.1/24 o.ä. müßte man nur z.B. weiteren Windows-Servern in der Firma eintragen, mit dem Ziel dieses Windows-VPN-Endpunkts.
Hexenwerk ist es nicht und externe Ressourcen braucht man offenkundig nicht, da ja der Server nach Log problemlos erreicht wird.
HG
Mark
aber: 10.8.0.1 ist der Windows-Server über das Tunnelnetz,
10.8.0.6 (dynamisch zugeordnet) ist der VPN-Client,
d.h. ein ping auf den Server sollte gehen und z.B. RDP-Zugang zu diesem auch bereits,
wenn es nur um Datei-Freigaben auf diesem Server geht, bist Du bereits fertig, 10.8.0.1 wird die allen vier Clients zur Verfügung stellen.
Eine weitere statische Route zu 10.8.0.1/24 o.ä. müßte man nur z.B. weiteren Windows-Servern in der Firma eintragen, mit dem Ziel dieses Windows-VPN-Endpunkts.
Hexenwerk ist es nicht und externe Ressourcen braucht man offenkundig nicht, da ja der Server nach Log problemlos erreicht wird.
HG
Mark
Ich habe (meiner laienhaften Meinung nach) die VPN-Verbindung via OpenVPN hergestellt,
Das ist auch genau richtig ! Zudem ist es die schnellste und unkomplizierteste Möglichkeit schnell einen Home Office Betrieb zu realisieren sofern du keine aktiven VPN Funktionen auf deinem Internet Router hast wie z.B. einer FritzBox.So muss dein Design aussehen auf der Server Seite ! (Auf deine IP Adressierung anpassen.)
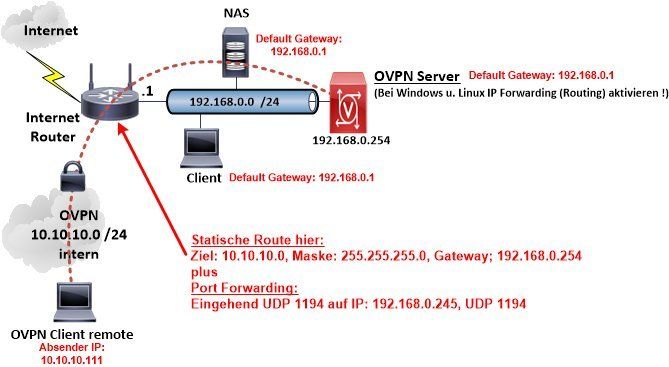
Das in der Zeichnung lokale LAN 192.168.0.0 /24 entspricht hier deinem lokalen LAN 192.168.10.0 /24
Das interne OVPN IP Netz der Zeichnung 10.10.10.0 /24 entspricht deinem 10.8.0.0 /24
Hier kannst du schon an der Zeichnung die allerwichtigsten ToDos sehen:
- Unbedingt einzurichten ist ein Port Forwarding auf dem Internet Router das dir den eingehenden OVPN Traffic mit UDP 1194 auf den internen OVPN Server sicherstellt. (Siehe o.a. Zeichnung)
- Weiterhin zwingend ist eine statische Route auf das interne OVPN Netz auf dem Internet Router. (Siehe o.a. Zeichnung)
dev tun
proto udp4
port 1194
ca /etc/openvpn/server/ca.crt
cert /etc/openvpn/server/test-server.crt
key /etc/openvpn/server/test-server.key
dh /etc/openvpn/server/dh.pem
cipher AES-256-CBC
auth SHA256
server 10.8.8.0 255.255.255.0
persist-key
persist-tun
topology subnet
push "topology subnet"
push "route 192.168.10.0 255.255.255.0"
keepalive 10 120
explicit-exit-notify 1
Die passende Client Konfig dann dazu:
dev tun
proto udp4
remote x.y.z.c 1194 => Remote OpenVPN Servername oder IP Addresse oder DynDNS Name des Routers
ca ca.crt
cert client3.crt
key client3.key
cipher AES-256-CBC
auth SHA256
auth-nocache
tls-client
remote-cert-tls server
persist-tun
persist-key
mute-replay-warnings
verb 1
auth-user-pass auth.cfg => Optional wenn Zertifikats Passwörter vergeben
Details zum Windows Client Setup auch hier.
Deine Log Messages sehen gut aus was die Peer connection anbetrifft. Die Zertifikats Erstellung ist also sehr wahrscheinlich OK.
Achtung hier in einem Windows Umfeld !
Folgende wichtige Windows spezifische Punkte sind zu beachten. Ursache ist so gut wie immer die Windows Firewall auf Server und auf Client Seite.
- Meist schlägt wegen des fehlenden Gateways die Windows Netzwerk Erkennung für den internen VPN Netzwerk Adapter fehl. Die Windows Firewall deklariert dann das OVPN Netzwerk als Public/Öffentlich und blockt damit dann sämtliche Verbindungen ! Hier musst du in das Setup Windows Firewall mit erweiterten Eigenschaften gehen und das Netzwerk Profil des VPN Adapters dort unbendingt auf Privat setzen ! Das gilt für Server und Client Rechner.
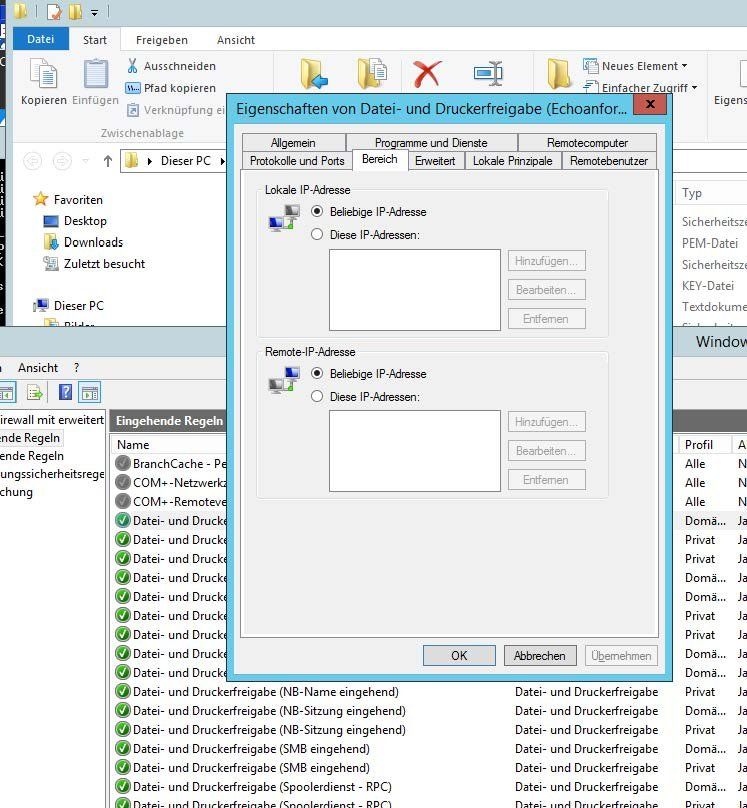
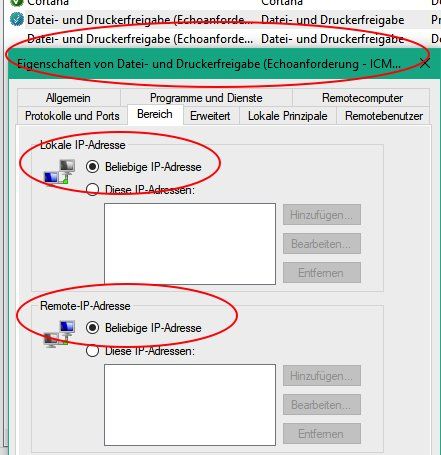
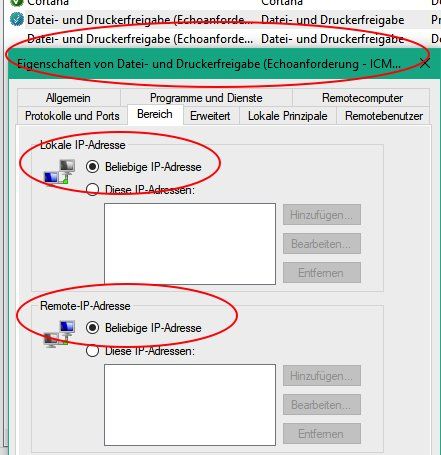
- ICMP (Ping) ist im Default geblockt in der Windows Firewall ! Willst du einen Ping Check machen musst du das also erst freigeben: windowspro.de/wolfgang-sommergut/ping-windows-10-erlauben-gui-po ... und auch die Adressbereich dort beidseitig aus Beliebig setzen.
- Desweiteren blockt die Windows Firewall per default alle Zugriffe mit fremden IP Adressen. Ggf. muss man hier also Sharing und Printer Dienste ebenfalls noch auf das OVPN IP Netz anpassen.
Wenn du das alles beachtest rennt das vollkommen fehlerfrei auf Anhieb.
Das lokale Port Forwwarding, statische Routing und Anpassen wer Firewall muss ebenso bei Wirequard passieren. Es ist alo keinerlei Arbeitserleichterung und schlimmer noch Wireguard ist derzeit in einem experimentellen Beta Status. Das als Home Office VPN einzusetzen für Mitarbeiter ist also extrem kontraproduktiv !
Du hast hier mit der Wahl von OpenVPN alles richtig gemacht. Zudem ist das erheblich besser in alle bekannten Betriebssysteme integriert wie auch Smartphones usw.
Grundlagen zu OpenVPN auch hier:
OpenVPN Server installieren auf pfSense Firewall, Mikrotik. DD-WRT oder GL.inet Router
Ist dann vermutlich das ICMP Blocking in der lokalen Windows Firewall was nicht richtig eingestellt ist.
 Und unter Allgemein musst du diese Regel für alle Profile zulassen.
Und unter Allgemein musst du diese Regel für alle Profile zulassen.
Wenn du mit aktivem Client pingst, dann solltest du zuallererst das VPN Interface des OVPN Servers 10.8.0.1 pingen. Das sollte immer und unter allen Umständen klappen.
Dann das lokale LAN Interface des OVPN Servers 192.168.10.6.
Diese beiden IPs müssen zwingend pingbar sein, denn das verifiziert dann die richtige Funktion des VPN Servers.
Hilfreich für ein zielgerichtetes Troubleshooting wäre es hier auch wenn du zur Kontrolle einmal deine Server- und Client OVPN Konfig Dateien hier anonymisiert posten würdest !
Wenn du mit aktivem Client pingst, dann solltest du zuallererst das VPN Interface des OVPN Servers 10.8.0.1 pingen. Das sollte immer und unter allen Umständen klappen.
Dann das lokale LAN Interface des OVPN Servers 192.168.10.6.
Diese beiden IPs müssen zwingend pingbar sein, denn das verifiziert dann die richtige Funktion des VPN Servers.
Hilfreich für ein zielgerichtetes Troubleshooting wäre es hier auch wenn du zur Kontrolle einmal deine Server- und Client OVPN Konfig Dateien hier anonymisiert posten würdest !