Pix 501 VPN Problem im Home Office
Hallo,
ich stehe gerade auf dem Schlauch.
Will in meinem Home Office den Zugriff von remote ermöglichen.
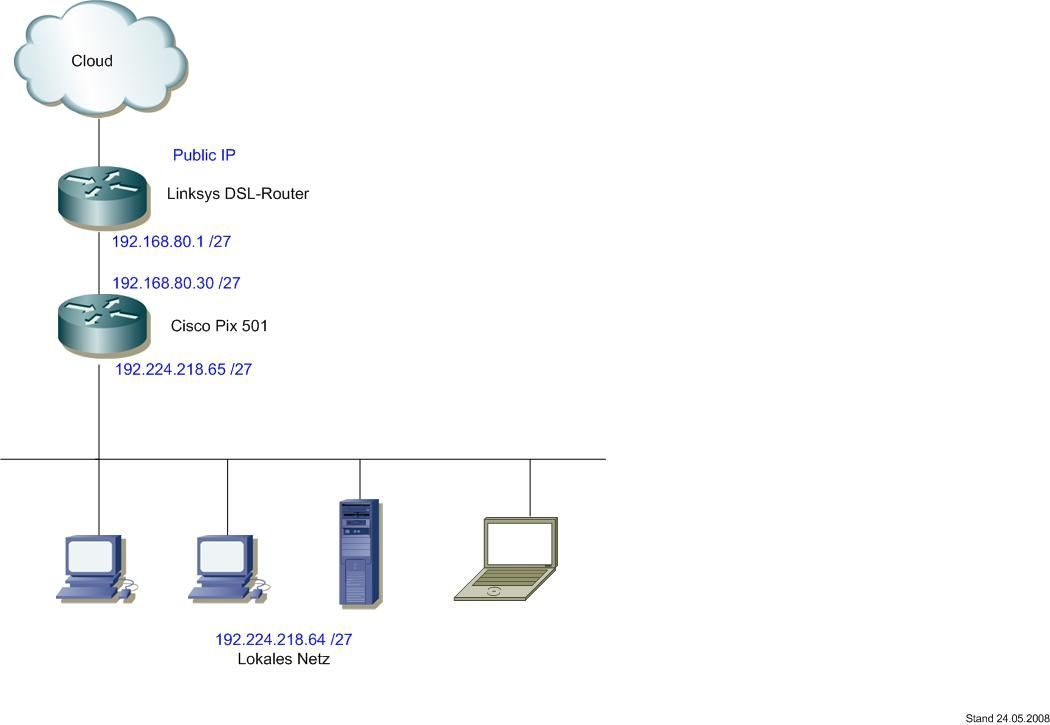
Netzwerk sieht im groben so aus, ein Linksys DSL Router macht die Internet Einwahl, so daß ich surfen kann. Das Linksys Teil macht VPN-Passthrough und reicht den VPN Traffic an die dahinter liegende Pix 501 weiter.
Verbinde ich mich nun von einem anderem Standort mit dem Cisco VPN Client so klappt der Tunnelaufbau, bekomme eine IP aus dem pool und das gewollte LAN (LAN hinter der Pix) steht in secured routes im client.
User Authentifizierung funktioniert lokal über die Pix, keine Radius Server oder ähnliches.
Soweit so gut. Will ich aber jetzt auf ein Host im LAN zugreifen kommt es zum Fehler.
Für mich sieht meine Config gut, die 2. vpngroup gibts nur weil ich herum probiert habe.
Sieht jemand den Fehler, liegt es eventuell am nat0?
Gruss Roland
Poste mal meine Config (mit Bild):
ich stehe gerade auf dem Schlauch.
Will in meinem Home Office den Zugriff von remote ermöglichen.
Netzwerk sieht im groben so aus, ein Linksys DSL Router macht die Internet Einwahl, so daß ich surfen kann. Das Linksys Teil macht VPN-Passthrough und reicht den VPN Traffic an die dahinter liegende Pix 501 weiter.
Verbinde ich mich nun von einem anderem Standort mit dem Cisco VPN Client so klappt der Tunnelaufbau, bekomme eine IP aus dem pool und das gewollte LAN (LAN hinter der Pix) steht in secured routes im client.
User Authentifizierung funktioniert lokal über die Pix, keine Radius Server oder ähnliches.
Soweit so gut. Will ich aber jetzt auf ein Host im LAN zugreifen kommt es zum Fehler.
Für mich sieht meine Config gut, die 2. vpngroup gibts nur weil ich herum probiert habe.
Sieht jemand den Fehler, liegt es eventuell am nat0?
Gruss Roland
Poste mal meine Config (mit Bild):
: Saved
: Written by enable_15 at 20:25:35.394 UTC Sat May 24 2008
PIX Version 6.3(5)
interface ethernet0 auto
interface ethernet1 100full
nameif ethernet0 outside security0
nameif ethernet1 inside security100
enable password xxxxxxxxxxxxxxx encrypted
passwd xxxxxxxxxxxxxx encrypted
hostname pix501
domain-name pix.tux
fixup protocol dns maximum-length 512
fixup protocol ftp 21
fixup protocol h323 h225 1720
fixup protocol h323 ras 1718-1719
fixup protocol http 80
fixup protocol ils 389
fixup protocol rsh 514
fixup protocol rtsp 554
fixup protocol sip 5060
fixup protocol sip udp 5060
fixup protocol skinny 2000
fixup protocol smtp 25
fixup protocol sqlnet 1521
fixup protocol tftp 69
names
access-list acl-inside permit ip any any
access-list acl-outside permit ip 192.168.20.0 255.255.255.240 192.224.218.64 255.255.255.224
access-list acl-outside permit tcp 192.168.20.0 255.255.255.240 192.224.218.64 255.255.255.224
access-list acl-outside permit ip 192.168.20.0 255.255.255.240 interface inside
access-list vpn-schmid_splitTunnelAcl permit ip 192.224.218.64 255.255.255.224 any
access-list inside_outbound_nat0_acl permit ip 192.224.218.64 255.255.255.224 192.168.20.0 255.255.255.240
access-list outside_cryptomap_dyn_20 permit ip any 192.168.20.0 255.255.255.240
access-list vpn-schmid2_splitTunnelAcl permit ip 192.224.218.64 255.255.255.224 any
access-list outside_cryptomap_dyn_40 permit ip any 192.168.20.0 255.255.255.240
pager lines 24
logging on
mtu outside 1500
mtu inside 1500
ip address outside 192.168.80.30 255.255.255.224
ip address inside 192.224.218.65 255.255.255.224
ip verify reverse-path interface outside
ip verify reverse-path interface inside
ip audit info action alarm
ip audit attack action alarm
ip local pool pool-schmid 192.168.20.1-192.168.20.10
pdm location 192.224.218.66 255.255.255.255 inside
pdm location 192.224.218.67 255.255.255.255 inside
pdm location 192.224.218.87 255.255.255.255 inside
pdm location 192.224.218.70 255.255.255.255 inside
pdm logging informational 100
pdm history enable
arp timeout 14400
global (outside) 1 interface
nat (inside) 0 access-list inside_outbound_nat0_acl
nat (inside) 1 0.0.0.0 0.0.0.0 0 0
access-group acl-outside in interface outside
access-group acl-inside in interface inside
route outside 0.0.0.0 0.0.0.0 192.168.80.1 1
timeout xlate 0:05:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 rpc 0:10:00 h225 1:00:00
timeout h323 0:05:00 mgcp 0:05:00 sip 0:30:00 sip_media 0:02:00
timeout sip-disconnect 0:02:00 sip-invite 0:03:00
timeout uauth 0:05:00 absolute
aaa-server TACACS+ protocol tacacs+
aaa-server TACACS+ max-failed-attempts 3
aaa-server TACACS+ deadtime 10
aaa-server RADIUS protocol radius
aaa-server RADIUS max-failed-attempts 3
aaa-server RADIUS deadtime 10
aaa-server LOCAL protocol local
http server enable
http 192.224.218.66 255.255.255.255 inside
http 192.224.218.67 255.255.255.255 inside
http 192.224.218.70 255.255.255.255 inside
no snmp-server location
no snmp-server contact
snmp-server community public
no snmp-server enable traps
floodguard enable
sysopt connection permit-ipsec
crypto ipsec transform-set ESP-3DES-MD5 esp-3des esp-md5-hmac
crypto dynamic-map outside_dyn_map 20 match address outside_cryptomap_dyn_20
crypto dynamic-map outside_dyn_map 20 set transform-set ESP-3DES-MD5
crypto dynamic-map outside_dyn_map 40 match address outside_cryptomap_dyn_40
crypto dynamic-map outside_dyn_map 40 set transform-set ESP-3DES-MD5
crypto map outside_map 65535 ipsec-isakmp dynamic outside_dyn_map
crypto map outside_map client authentication LOCAL
crypto map outside_map interface outside
isakmp enable outside
isakmp policy 20 authentication pre-share
isakmp policy 20 encryption 3des
isakmp policy 20 hash md5
isakmp policy 20 group 2
isakmp policy 20 lifetime 86400
vpngroup vpn-schmid address-pool pool-schmid
vpngroup vpn-schmid dns-server 80.242.134.56 80.242.134.56
vpngroup vpn-schmid split-tunnel vpn-schmid_splitTunnelAcl
vpngroup vpn-schmid idle-time 1800
vpngroup vpn-schmid password xxxxxxxxx
vpngroup vpn-schmid2 address-pool pool-schmid
vpngroup vpn-schmid2 dns-server 80.242.134.56
vpngroup vpn-schmid2 split-tunnel vpn-schmid2_splitTunnelAcl
vpngroup vpn-schmid2 idle-time 1800
vpngroup vpn-schmid2 password xxxxxxxxxxxxxx
telnet timeout 5
ssh timeout 5
console timeout 0
dhcpd lease 3600
dhcpd ping_timeout 750
dhcpd auto_config outside
username roland password xxxxxxxxxx encrypted privilege 15
username roland2 password xxxxxxxxxxx encrypted privilege 15
terminal width 80
Cryptochecksum:xxxxxxxxxxx
: end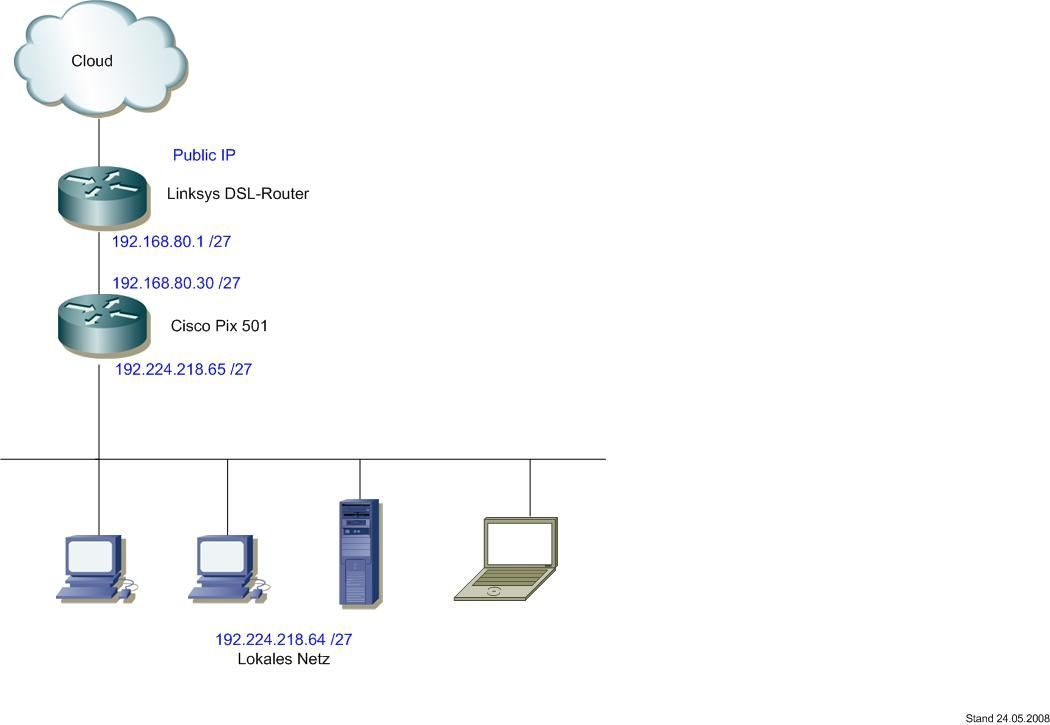
Bitte markiere auch die Kommentare, die zur Lösung des Beitrags beigetragen haben
Content-ID: 88386
Url: https://administrator.de/forum/pix-501-vpn-problem-im-home-office-88386.html
Ausgedruckt am: 05.07.2025 um 19:07 Uhr