CISCO PIX 515 PIX Version 6.3(3) PDM Version 3.0(1)
Zugriff auf Device Manager
Hallo,
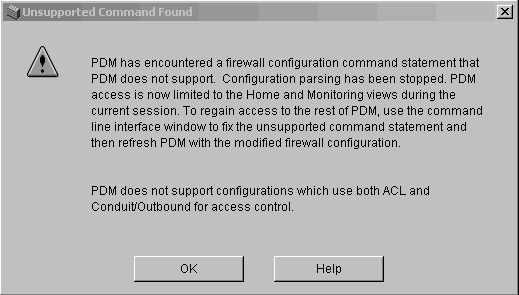
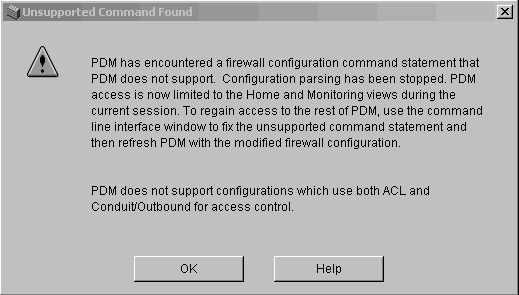
ich habe ein Problem beim Zugriff auf den Device Manager, soweit geht alles nur kann ich mir die Konfiguration nicht anzeigen lassen und bekomme immer anhängenden Fehler. Vielleicht kennt jemand den Fehler und kann mir sagen woran es liegt.
Vielen Dank
Hallo,
ich habe ein Problem beim Zugriff auf den Device Manager, soweit geht alles nur kann ich mir die Konfiguration nicht anzeigen lassen und bekomme immer anhängenden Fehler. Vielleicht kennt jemand den Fehler und kann mir sagen woran es liegt.
Vielen Dank
Bitte markiere auch die Kommentare, die zur Lösung des Beitrags beigetragen haben
Content-ID: 104612
Url: https://administrator.de/forum/cisco-pix-515-pix-version-6-33-pdm-version-3-01-104612.html
Ausgedruckt am: 20.07.2025 um 04:07 Uhr
3 Kommentare
Neuester Kommentar
PDM does not support configurations which use both ACL and Conduit/outbound for access control.
So weit ich diese Fehlermeldung interpretiere hast du eine ACL definiert und zusätzlich eine Outbound Regel. Der PDM kann nicht damit umgehen wenn beides in deiner Konfig auftaucht. Such mal nach einer Zeile wie:
Outbound 30 permit 0.0.0.0 0.0.0.0 tcp 0
und überlege dir ob das Sinn macht oder was zuletzt geändert wurde.
In deiner Config steht:
Wenn du den PDM verwenden möchtest musst du dich entscheiden, entweder ACL oder Counduit (durchleiten)
Im Cisco Handbuch steht dazu:
cisco.com/en/US/docs/security/pix/pix63/command/reference/cmdref ...
access-group acl_outside in interface outside
conduit permit icmp any any
conduit permit icmp any any
Wenn du den PDM verwenden möchtest musst du dich entscheiden, entweder ACL oder Counduit (durchleiten)
Im Cisco Handbuch steht dazu:
cisco.com/en/US/docs/security/pix/pix63/command/reference/cmdref ...
conduit
Add, delete, or show conduits through the PIX Firewall for incoming connections. However, the conduit command has been superseded by the access-list command. We recommend that you migrate your configuration away from the conduit command to maintain future compatibility.
Add, delete, or show conduits through the PIX Firewall for incoming connections. However, the conduit command has been superseded by the access-list command. We recommend that you migrate your configuration away from the conduit command to maintain future compatibility.